DAFORMS.NET – DA FORM 137-2 – Installation Clearance Record – The Department of the Army (DA) Form 137-2, also known as the Installation Clearance Record, is an important document used by U.S. military personnel to keep track of their access clearances for security purposes. This form is critical for ensuring that service members have the appropriate levels of clearance for accessing sensitive information and facilities at military installations.
Download DA FORM 137-2 – Installation Clearance Record
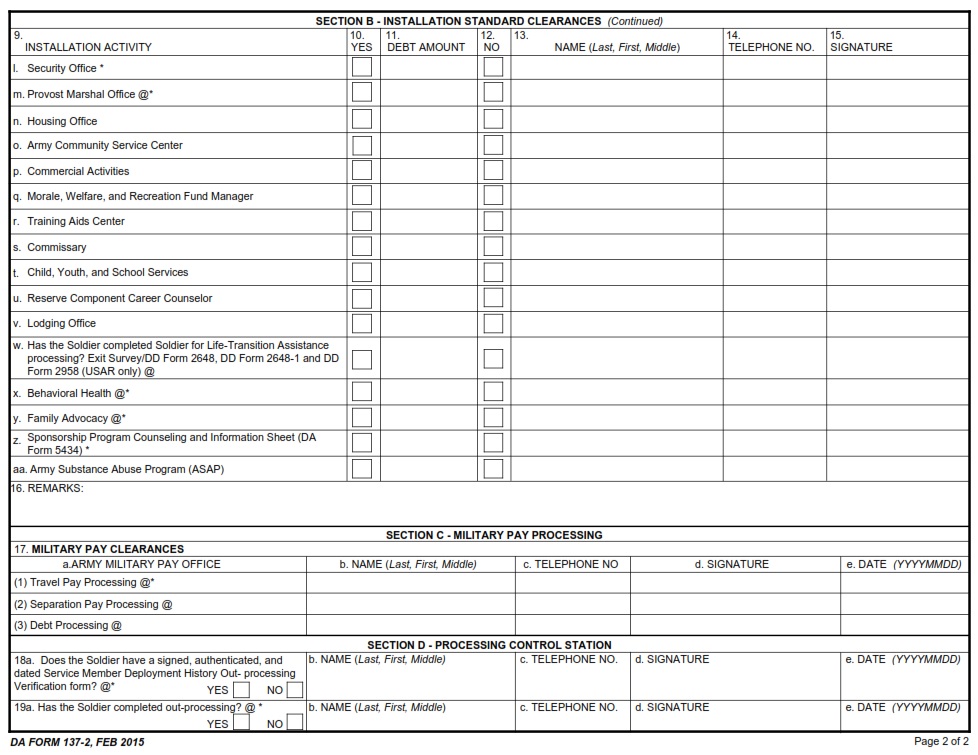
| Form Number | DA FORM 137-2 |
| Form Title | Installation Clearance Record |
| Published | 02/01/2015 |
| Prescribing Pub | AR 600-8-101 |
| File Size | 51 KB |
DA FORM 137-2 (30480 downloads )
What is a DA FORM 137-2?
This article is about the Department of the Army form, DA Form 137-2, which serves as an installation clearance record. This document is used by military personnel when leaving a particular installation or base.
It allows them to show proof that their service obligations have been met and that they are eligible for separation from active duty. This form also serves as proof of service at specific duty locations and can be used for a variety of reasons, such as obtaining veteran benefits or employment in the civilian sector.
Where Can I Find a DA FORM 137-2?
Having a secure installation is essential to the success of any military mission. To ensure that security, the Department of the Army (DA) developed Form 137-2 – Installation Clearance Record, also known as the Visitor Access Request form.
This form must be filled out and submitted in order for an individual to gain access to a secure Army installation. The DA Form 137-2 provides all necessary information about the visitor and is used to verify identity and approve visitor access on installations.
DA FORM 137-2 – Installation Clearance Record
The importance of maintaining an accurate and up-to-date Installation Clearance Record cannot be overstated. The DA Form 137-2 is a document used by the United States Department of Defense to keep track of security clearances for military personnel and civilians employed by the government. It is a critical component in ensuring that only individuals who are authorized to access sensitive information are given access to it.